Hackers Using OAuth Apps in Microsoft Entra ID to Establish Persistence

Hackers Using OAuth Apps in Microsoft Entra ID Hackers are increasingly abusing OAuth applications in Microsoft Entra ID to gain persistent access, blending in as normal “business integrations” while keeping access even after defenders reset passwords. Recent Wiz research and incident reporting show attackers using fake OAuth apps, deceptive consent prompts, and redirect URLs to steal tokens […]
Adidas Investigates Alleged Data Breach 815,000 Records of Customer Data Stolen

Adidas has confirmed it is actively investigating a potential data breach involving one of its independent third-party partners after a threat actor operating under the alias “LAPSUS-GROUP” posted claims on BreachForums on February 16, 2026, alleging unauthorized access to the sportswear giant’s extranet portal. The actor, believed to be associated with the Scattered Lapsus$ Hunters […]
Selective Thread Emulation and Fuzzing Expose DoS Flaws in Socomec DIRIS M-70 IIoT Device

Security researchers have uncovered six critical denial-of-service vulnerabilities in the Socomec DIRIS M-70 industrial gateway used for power monitoring and energy management in critical infrastructure. The flaws were discovered through an innovative emulation technique that bypassed hardware debugging limitations by focusing on a single thread handling Modbus protocol communications. The M-70 gateway facilitates data communication […]
Microsoft Teams to Prompt Mobile Users for Browser Choice with Non-Office and PDF Links
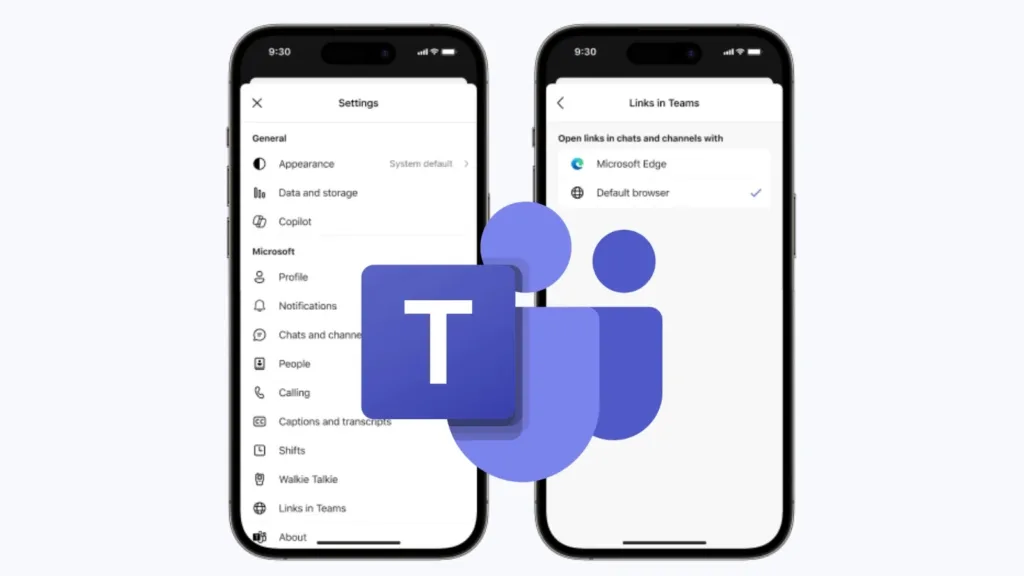
Microsoft is rolling out a significant update to Teams Mobile on Android and iOS that changes how non-Office and PDF links are handled within the app. Beginning in late February 2026, users will be presented with a browser selection prompt when tapping links to files that aren’t Office documents (Word, Excel, or PowerPoint) or PDFs. […]
Cryptocurrency Scams Target Asia, Combining Malvertising and Pig Butchering with Losses Up to 10 Million

A sophisticated cryptocurrency scam campaign is currently targeting users across Asia, with a heavy and specific focus on Japan. This operation uniquely combines two distinct fraud models into a single, highly effective attack vector: malvertising and “pig butchering.” By blending the broad reach of malicious advertising with the psychological manipulation of long-term social engineering, cybercriminals […]
New SysUpdate Variant Malware Discovered and Tool Developed to Decrypt Encrypted Linux C2 Traffic

A new variant of the SysUpdate malware has emerged as a sophisticated threat targeting Linux systems with advanced command-and-control (C2) encryption capabilities. The malware was discovered during a Digital Forensics and Incident Response (DFIR) engagement when security teams detected the suspicious Linux binary in a client’s environment. This packed ELF64 executable uses an unknown obfuscated […]
Notepad++ v8.9.2 Released with Double-Lock Update Mechanism Following Recent Hack
Notepad++ v8.9.2 Released The widely used open-source text and code editor has released version v8.9.2, introducing a major security enhancement known as the “Double-Lock” update mechanism. This update addresses vulnerabilities that were exploited in a recent state-sponsored attack targeting the application’s update infrastructure. Last month, Notepad++’s official site confirmed that attackers had successfully hijacked its update channel, allowing […]
Malware in the Wild as Malicious Fork of Legitimate Triton App Surfaces on GitHub

A malicious fork of the legitimate macOS application Triton has surfaced on GitHub, exploiting open-source repositories to distribute malware. The fraudulent repository, created under the account “JaoAureliano,” appeared as a copy of the original Triton app developed by Otávio C. Instead of providing genuine software, the fork redirected users to download a ZIP file containing […]
Malicious Chrome Extension Steals Facebook Business Manage 2FA Codes and Analytics Data
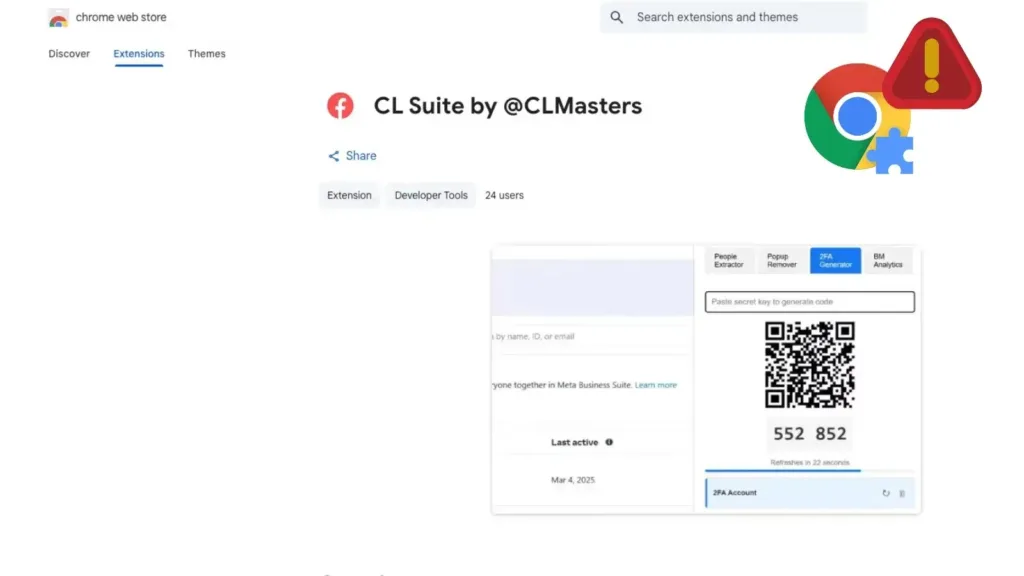
Malicious Chrome Extension Steals Facebook Business Manage 2FA Codes A malicious Chrome extension that claims to help Meta Business users quietly steals Facebook Business Manager 2FA codes and analytics data, putting high‑value ad accounts at risk of takeover. The extension, “CL Suite by @CLMasters” (ID: jkphinfhmfkckkcnifhjiplhfoiefffl), is still available in the Chrome Web Store and specifically […]
Noodlophile Malware Creators Evolve Tactics with Fake Job Postings and Phishing Lures

The Noodlophile information stealer, originally uncovered in May 2025, has significantly evolved its attack strategies to bypass security measures. Initially, this malware hid behind deceptive advertisements for fake AI video generation platforms on social media, tricking users into downloading malicious ZIP files. These early campaigns focused on harvesting credentials and cryptocurrency wallets, which were then […]
