Hackers Exploiting Ivanti EPMM Devices to Deploy Dormant Backdoors

Ivanti EPMM Devices Exploited Hackers are actively exploiting Ivanti Endpoint Manager Mobile (EPMM) appliances to plant “dormant” backdoors that can sit unused for days or weeks. Ivanti recently disclosed two critical EPMM flaws, CVE-2026-1281 and CVE-2026-1340, spanning authentication bypass and remote code execution in different packages (aftstore and appstore). While the packages differ, defenders face […]
New Telegram Phishing Attack Abuses Authentication Workflows to Obtain Full Authorized User Sessions

A sophisticated Telegram phishing campaign has re-emerged, marking a significant evolution in how threat actors compromise user accounts. Unlike traditional credential harvesting, this operation does not rely on cloning login pages to steal passwords but instead manipulates the platform’s legitimate authentication infrastructure. By integrating directly with Telegram’s official login workflows, the attackers can bypass standard […]
Cybersecurity Weekly Newsletter Notepad++ hack, Office 0-Day, ESXi 0-day Ransomware Attacks and More

Cybersecurity Newsletter Weekly February Welcome to this week’s pulse on the cyber threat landscape, where vulnerabilities strike fast, and defenders must move faster. Notepad++ users face a supply-chain nightmare after a malicious update; Microsoft Office’s latest 0-day is ripe for exploitation; and ESXi servers are under siege from ruthless ransomware gangs. We’ve dissected these incidents, […]
LocalGPT A Secure Local Device Focused AI Assistant Built in Rust
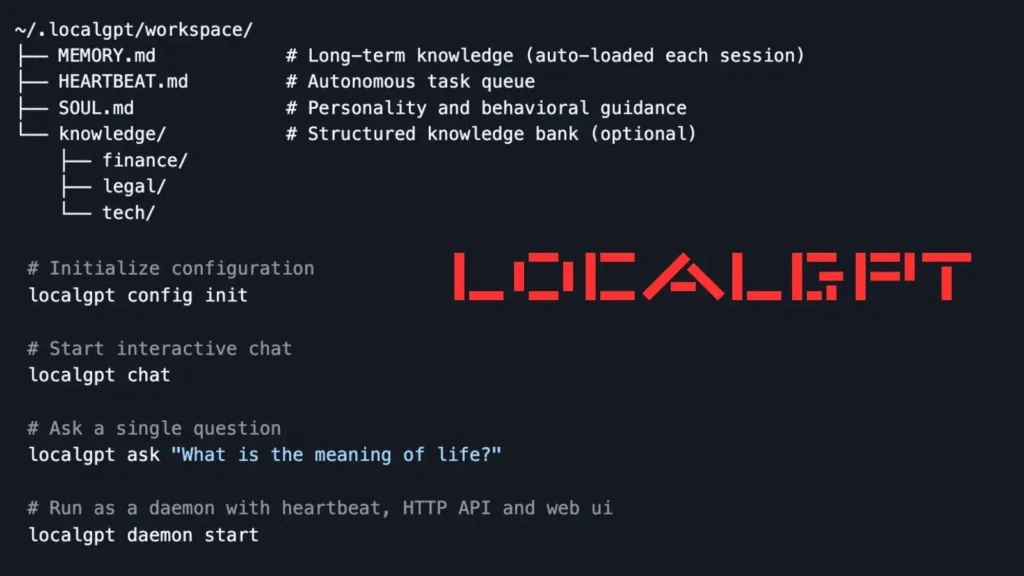
LocalGPT In an era where AI assistants like ChatGPT and Claude dominate cloud infrastructures, exposing user data to remote breaches, a new Rust-based tool called LocalGPT promises a fortress-like alternative. Developed as a single ~27MB binary, LocalGPT runs entirely on local devices, keeping sensitive memory and tasks off the cloud. Inspired by and compatible with […]
BridgePay Payment Gateway Hit by Ransomware, Causing Nationwide Outages

BridgePay Ransomware Attack BridgePay Network Solutions, a major U.S. payment gateway provider, confirmed a ransomware attack caused a widespread outage, disrupting card processing for merchants nationwide. The outage began early on February 6, 2026, around 3:29 a.m. EST with degraded performance in systems like the Gateway.Itstgate.com virtual terminal, reporting, and API. By 5:48 a.m. EST, […]
Hackers Linked to State Actors Target Signal Messages of Military Officials and Journalists

Hackers Target Signal Messages Military Officials Germany’s top security agencies issued an urgent warning yesterday regarding a sophisticated cyber espionage campaign targeting high-ranking officials and journalists across Europe. The Federal Office for the Protection of the Constitution (BfV) and the Federal Office for Information Security (BSI) revealed that state-sponsored hackers are hijacking Signal accounts to […]
nmapUnleashed Makes Nmap Scanning More Comfortable and Effective
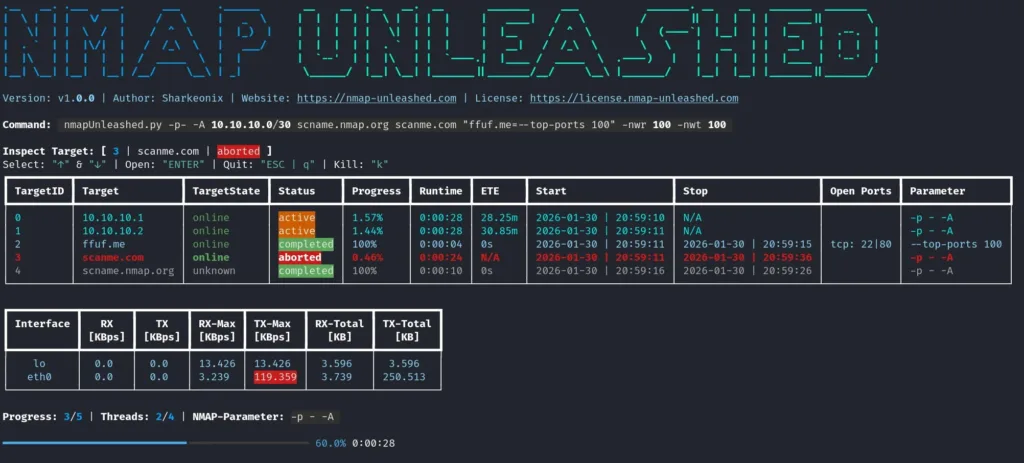
nmapUnleashed Tool nmapUnleashed emerges as a powerful CLI wrapper enhancing Nmap’s capabilities for penetration testers and network auditors. Released in late January 2026 by developer Sharkeonix, this open-source tool streamlines complex scans while retaining full Nmap compatibility. nmapUnleashed, or “nu,” wraps Nmap to add multithreading, allowing up to customizable parallel scans (default 4 threads) for […]
Transparent Tribe Hacker Group Attacking Indias Startup Ecosystem
The threat landscape for India’s technology sector has taken an unexpected turn. A Pakistan-based hacking group called Transparent Tribe has shifted its focus from traditional government targets to the country’s vibrant startup ecosystem, particularly companies working in cybersecurity and intelligence domains. The group, also tracked as APT36, has been active since 2013 and now uses […]
CISA Orders Removal of Active Network Edge Devices to Reduce Security Risks

CISA Removal of Edge Devices CISA has issued Binding Operational Directive (BOD) 26-02, ordering Federal Civilian Executive Branch (FCEB) agencies to eliminate “end of support” (EOS) edge devices from their networks. This directive, developed in coordination with the Office of Management and Budget (OMB), addresses the significant security risks posed by unsupported hardware that resides […]
Hackers Leveraging Windows Screensaver to Deploy RMM Tools and Gain Remote Access to Systems
Cybersecurity threats are constantly evolving, and a recent campaign highlights a deceptive new tactic where attackers leverage Windows screensaver (.scr) files to compromise systems. This method allows threat actors to deploy legitimate Remote Monitoring and Management (RMM) tools, granting them persistent remote access while effectively bypassing standard security controls. By utilizing trusted software and cloud […]
