Malware Operators Collaborate With Covert North Korean IT Workers to Attack Corporate Organizations

A sophisticated cybercriminal alliance between malware operators and covert North Korean IT workers has emerged as a significant threat to corporate organizations worldwide. This hybrid operation, known as DeceptiveDevelopment, represents a dangerous convergence of traditional cybercrime and state-sponsored activities, targeting software developers and cryptocurrency professionals through elaborate social engineering campaigns. The DeceptiveDevelopment group, active since […]
New YiBackdoor Allows Attackers to Execute Arbitrary Commands and Exfiltrate Sensitive Data from Hacked Systems

A sophisticated new malware family dubbed YiBackdoor has emerged in the cybersecurity landscape, posing a significant threat to organizations worldwide. First observed in June 2025, this malicious software represents a concerning evolution in backdoor technology, featuring advanced capabilities that enable threat actors to execute arbitrary commands, capture screenshots, collect sensitive system information, and deploy additional […]
CISA Warns of Google Chrome 0-Day Vulnerability Exploited in Attacks

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning about a high-severity zero-day vulnerability in Google Chrome that is being actively exploited in attacks. The vulnerability, tracked as CVE-2025-10585, has been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, signaling an urgent need for users and administrators to take action. Google has […]
Hackers Exploit WerFaultSecure.exe Tool to Steal Cached Passwords From LSASS on Windows 11 24H2

Threat actors are leveraging the legacy Windows error‐reporting utility WerFaultSecure.exe to extract the memory region of the Local Security Authority Subsystem Service (LSASS.EXE) and harvest cached credentials from fully patched Windows 11 24H2 systems. After gaining initial access to a host, adversaries frequently seek to dump LSASS memory to escalate privileges and move laterally across […]
Hackers Abusing GitHub Notifications to Deliver Phishing Emails

In recent weeks, security researchers have uncovered an elaborate phishing campaign that leverages legitimate GitHub notification mechanisms to deliver malicious content. Victims receive seemingly authentic repository alerts, complete with real-looking commit messages and collaborator updates. Upon closer inspection, the notification headers reveal altered sender addresses and obfuscated links. The campaign’s sophistication has allowed it to […]
Libraesva ESG Vulnerability Let Attackers Inject Malicious Commands

A critical security flaw in Libraesva ESG email security gateways has been identified and patched, allowing threat actors to execute arbitrary commands through specially crafted email attachments. The vulnerability, tracked as CVE-2025-59689, affects multiple versions of the popular email security platform and has already been exploited by what security researchers believe to be a foreign […]
European Airport Disruptions Caused by Sophisticated Ransomware Attack

Over the weekend, a sophisticated ransomware attack compromised Collins Aerospace’s Muse check-in and boarding systems, forcing key hubs including Heathrow, Brussels, and Berlin to return to manual processes. Airlines reported hundreds of delayed and cancelled flights as security teams raced to contain the breach, restore encrypted data, and deploy software patches. The Guardian stated that […]
Hackers Bypassing Windows Mark of the Web Files Using LNK Stomping Attack
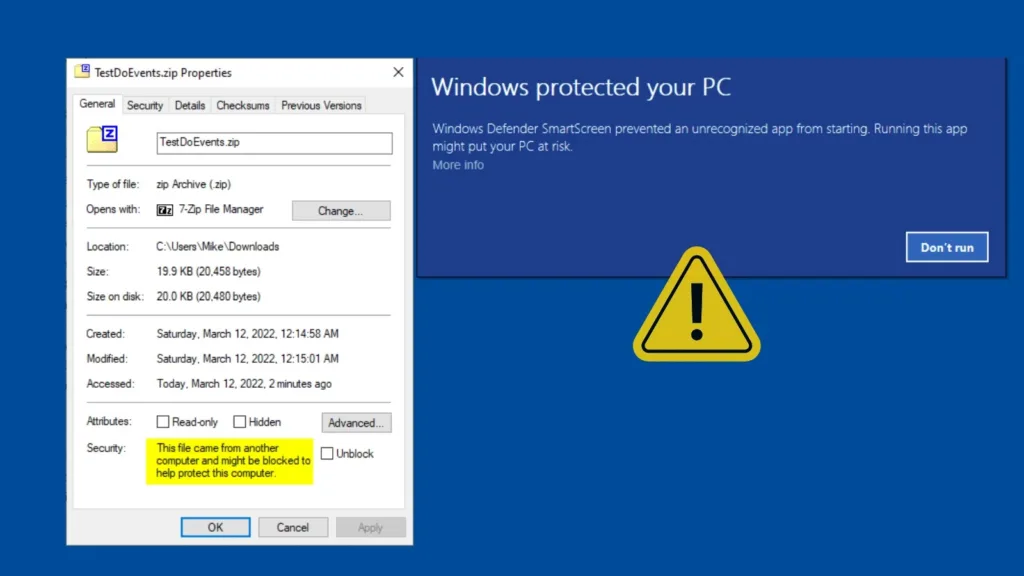
A sophisticated attack technique called LNK Stomping has emerged as a critical threat to Windows security, exploiting a fundamental flaw in how the operating system handles shortcut files to bypass security controls. Designated as CVE-2024-38217 and patched on September 10, 2024, this vulnerability demonstrates how attackers can manipulate Windows shortcuts (LNK files) to circumvent the […]
Massive Cyber-Attack Attacking macOS Users via GitHub Pages to Deliver Stealer Malware
A sophisticated cyber-attack campaign exploiting GitHub Pages to distribute the notorious Atomic stealer malware to macOS users. The threat actors behind this operation are leveraging Search Engine Optimization (SEO) techniques to position malicious repositories at the top of search results across major platforms, including Google and Bing, targeting users searching for legitimate software from technology […]
BlackLock Ransomware Attacking Windows, Linux, and VMware ESXi Environments
A sophisticated new ransomware operation dubbed BlackLock has emerged as a significant threat to organizations worldwide, demonstrating advanced cross-platform capabilities and targeting diverse computing environments. Originally operating under the name “El Dorado” since March 2024, the group rebranded to BlackLock in September 2024, establishing itself as a formidable player in the ransomware landscape with victims […]
