Critical Vulnerability in Next-Mdx-Remote Allows Arbitrary Code Execution in React Server-Side Rendering

Vulnerability in Next-Mdx-Remote Security advisory HCSEC-2026-01 revealed a critical vulnerability in the next-mdx-remote library that allows attackers to execute arbitrary code on servers rendering untrusted MDX content. Tracked as CVE-2026-0969, the issue affects versions 4.3.0 through 5.0.0 and is fixed in 6.0.0. Next-mdx-remote is a popular open-source TypeScript library for Next.js based React apps. It […]
Odido Telecom Suffers Cyberattack 6.2 Million Customer Accounts Affected

Odido Telecom Suffers Cyberattack Odido Telecom, a leading Dutch telecommunications provider, confirmed on February 12, 2026, that hackers accessed personal data from 6.2 million customer accounts in a major cyberattack. The breach, detected over the February 7-8 weekend, has raised alarms about phishing risks despite no disruption to services. Hackers infiltrated Odido’s customer relationship management […]
Rogue VM Linked to Muddled Libra in VMware vSphere Attack, Revealing Key TTPs
In a September 2025 incident response case, investigators found a rogue virtual machine inside a VMware vSphere environment and tied it with high confidence to Muddled Libra, also tracked as Scattered Spider and UNC3944. The VM acted like a quiet staging host, giving the intruders a place to recon the network, pull down tools, and […]
Palo Alto Networks Firewall Vulnerability Allows an Attacker to Force Firewalls into a Reboot Loop

Palo Alto Networks Firewall Vulnerability A critical denial-of-service (DoS) flaw in Palo Alto Networks’ PAN-OS software could let unauthenticated attackers crash firewalls into endless reboot cycles, potentially crippling enterprise networks. Dubbed CVE-2026-0229, the vulnerability lurks in the Advanced DNS Security (ADNS) feature. An attacker sends a maliciously crafted packet to trigger a system reboot. Repeated […]
VoidLink Framework Enables On-Demand Tool Generation with Windows Plugin Support

A newly tracked intrusion framework called VoidLink is drawing attention for its modular design and focus on Linux systems. It behaves like an implant management framework, letting operators deploy a core implant and add capabilities as needed, which shortens the time from access to action. Recent activity has been linked to a threat actor Cisco […]
Legacy IRC Botnet Campaign Uses Automated SSH Compromise Pipeline to Enroll Linux Hosts at Scale
SSHStalker is a newly discovered Linux botnet that brings back Internet Relay Chat (IRC) control while using automation to compromise servers over SSH. It mainly succeeds by guessing weak or reused passwords, then turning each host into a launchpad for more scans and installs. In honeypot intrusions seen in early 2026, attackers dropped a Golang […]
Socelars Malware Attacking Windows Systems to Steal Sensitive Business Data
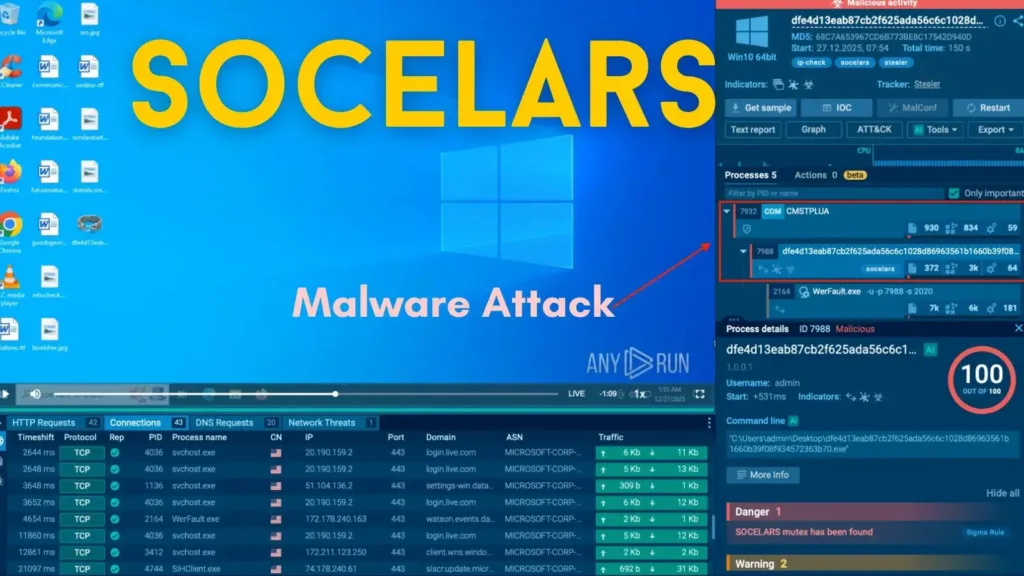
Socelars Malware Attacking Windows Systems A dangerous information-stealing malware called Socelars is actively targeting Windows systems to collect sensitive authentication data, with particular focus on Facebook Ads Manager accounts and session cookies. Unlike traditional malware that causes immediate system damage, Socelars operates silently in the background, turning infected machines into gateways for account takeover and […]
Microsoft Patch Tuesday February 2026 54 Vulnerabilities Fixed, Including 6 Zero-days
Microsoft Patch Tuesday February 2026 Microsoft released its February 2026 Patch Tuesday updates on February 10, addressing 54 vulnerabilities, including six zero-days across Windows, Office, Azure, and developer tools. The updates fix issues in products like Windows Remote Desktop Services, Microsoft Defender, Azure services, GitHub Copilot, Visual Studio Code, Microsoft Exchange, and Office apps. Severity […]
Hackers Weaponizing 7-Zip Downloads to Turn Your Home Computers into Proxy Nodes

A deceptive campaign targeting unsuspecting users has emerged, using a counterfeit version of the widely used 7-Zip file archiving software to silently transform home computers into residential proxy nodes. The malicious operation relies on a lookalike domain, 7zip[.]com, which closely mimics the legitimate 7-zip.org website, tricking users into downloading a compromised installer that appears fully […]
AI Chat App Exposes 300 Million Messages from 25 Million Users

AI Chat App Exposes Messages The popular mobile application “Chat & Ask AI” has inadvertently exposed hundreds of millions of private user conversations. The app, which boasts over 50 million users across the Google Play and Apple App stores, failed to secure its backend database, allowing unauthorized access to sensitive user data. The leak stemmed […]
