Google Announces Android Theft Protection Feature to Make Your Device Harder Target for Hackers

Google has rolled out a comprehensive update to Android’s theft protection capabilities, introducing stronger authentication safeguards and enhanced recovery tools designed to protect users before, during, and after theft attempts. The multi-layered defense system, announced on January 26, 2026, builds on existing protections and aims to transform Android devices into significantly harder targets for criminals. […]
Swarmer Tool Evading EDR With a Stealthy Modification on Windows Registry for Persistence

Praetorian Inc. has publicly released Swarmer, a tool enabling low-privilege attackers to achieve stealthy Windows registry persistence by sidestepping Endpoint Detection and Response (EDR) monitoring. Deployed operationally since February 2025, Swarmer exploits mandatory user profiles and the obscure Offline Registry API to modify the NTUSER hive without triggering standard registry hooks. Traditional registry persistence via […]
Threat Actors Leverage Real Enterprise Email Threads to Deliver Phishing Links
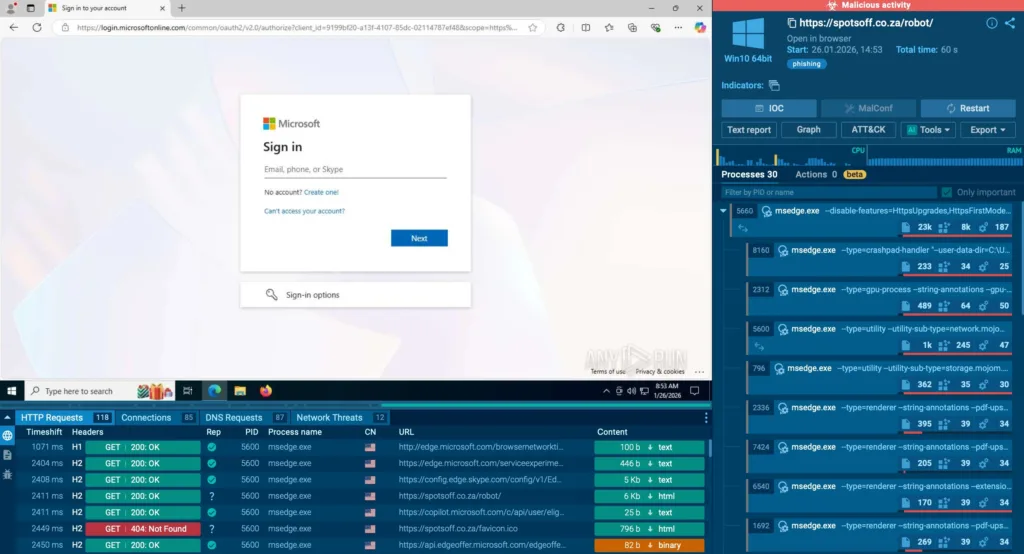
In a sophisticated supply chain phishing attack, threat actors hijacked an ongoing email thread among C-suite executives discussing a document awaiting final approval. The intruder, posing as a legitimate participant, replied directly with a phishing link mimicking a Microsoft authentication form. Researchers attribute this to a compromised sales manager account at an enterprise contractor, allowing […]
ZAP JavaScript Engine Memory Leak Issue Impacts Active Scan Usage
The ZAP (Zed Attack Proxy) project, a widely used open-source web application security scanner, has disclosed a critical memory leak in its JavaScript engine. This flaw, likely present for some time, now disrupts active scanning workflows following the introduction of a new JavaScript scan rule in the OpenAPI add-on. Security teams relying on ZAP for […]
Fake CAPTCHA Attack Leverages Microsoft Application Virtualization (App-V) to Deploy Malware
A newly discovered campaign demonstrates a sophisticated approach to delivering information-stealing malware through a combination of social engineering and legitimate Windows components. The attack begins with a deceptive CAPTCHA prompt that tricks users into executing commands manually through the Windows Run dialog, presenting the infection as a required verification step. Instead of using traditional PowerShell […]
Attackers Hijacking Official GitHub Desktop Repository to Distribute Malware as Official Installer

Cybercriminals have discovered a dangerous way to trick developers into downloading malware by exploiting how GitHub works. The attack involves creating fake versions of the GitHub Desktop installer and making them appear legitimate to unsuspecting users. Between September and October 2025, this campaign primarily targeted users in Europe and the European Economic Area, though infections […]
Attackers Exploiting React2Shell Vulnerability to Attack IT Sectors
Threat actors have started targeting companies in the insurance, e-commerce, and IT sectors through a critical vulnerability tracked as CVE-2025-55182, commonly known as React2Shell. This flaw exists in the Flight protocol that handles client-server communication for React Server Components, allowing attackers to run unauthorized code on vulnerable servers. The vulnerability originates from insecure deserialization, where […]
China-Aligned APTs Use PeckBirdy C&C Framework in Multi-Vector Attacks, Exploiting Stolen Certificates
Since 2023, a dangerous malware framework called PeckBirdy has emerged as a primary weapon used by Chinese-aligned hacking groups. This JavaScript-based tool serves as a command-and-control platform designed to work across multiple system environments, giving attackers remarkable flexibility in how they deploy their attacks. The framework targets victims in the gambling industry and government organizations […]
Nova Ransomware Allegedly Claiming Breach of KPMG Netherlands

A major accounting firm in the Netherlands has reportedly become the latest victim of Nova, an active ransomware operation. The breach was discovered and indexed by ransomware live on January 23, 2026, with the estimated attack date coinciding with the discovery date. The attackers claim to have exfiltrated sensitive data and have issued a 10-day […]
48M Gmail, 6.5M Instagram Exposed Online From Unprotected Database

A massive database containing 149 million stolen login credentials was discovered exposed online without password protection or encryption. Posing serious security risks to users of Gmail, Instagram, Facebook, Netflix, and thousands of other platforms worldwide. The publicly accessible database contained 149,404,754 unique logins and passwords harvested through infostealer malware and keylogging software. Each record included […]
