Finland Arrests Two Cargo Ship Crew Members Over Undersea Cable Damage

Finnish authorities have detained all 14 crew members of a cargo vessel suspected of deliberately damaging an undersea telecommunications cable connecting Helsinki to Estonia. The ship, named Fitburg, was sailing from St. Petersburg, Russia, to Haifa, Israel, under a St. Vincent and the Grenadines flag when the incident occurred. The crew, comprising Russian, Georgian, Kazakh, […]
VVS Stealer Uses PyArmor Obfuscation to Evade Static Analysis and Signature Detection

The cybersecurity landscape is witnessing a rise in sophisticated malware that leverages legitimate tools to mask malicious intent. A prime example is VVS Stealer (also styled VVS $tealer). This Python-based malware family has been actively marketed on Telegram since April 2025. This threat targets Discord users explicitly to exfiltrate sensitive credentials, tokens, and browser data. […]
10,000+ Fortinet Firewalls Still Exposed to 5-year Old MFA Bypass Vulnerability

Over 10,000 Fortinet firewalls worldwide remain vulnerable to CVE-2020-12812, a multi-factor authentication (MFA) bypass flaw disclosed over five and a half years ago. Shadowserver recently added the issue to its daily Vulnerable HTTP Report, highlighting persistent exposure amid active exploitation confirmed by Fortinet in late 2025. CVE-2020-12812 stems from improper authentication in FortiOS SSL VPN […]
Handala Hackers Targeted Israeli Officials by Compromising Telegram Accounts

In December 2025, the Iranian-linked hacking group Handala claimed to have fully compromised the mobile devices of two prominent Israeli political figures. However, detailed analysis by Kela cyber intelligence researchers revealed a more limited scope—the breaches targeted Telegram accounts specifically, not complete device access. The group claimed to have breached former Prime Minister Naftali Bennett’s […]
Hackers Abusing Google Tasks Notification for Sophisticated Phishing Attack

Hackers have launched a sophisticated phishing campaign exploiting Google Tasks notifications to target over 3,000 organizations worldwide, primarily in the manufacturing sector. The December 2025 attacks signal a dangerous shift in email-based threats, in which attackers abuse legitimate Google infrastructure rather than spoofing domains or forging email headers. The phishing emails originated from a legitimate […]
RondoDoX Botnet Weaponizing a Critical React2Shell Vulnerability to Deploy Malware
A sophisticated threat group has intensified its campaign against organizations by leveraging the latest vulnerabilities in web applications and Internet of Things (IoT) devices. The RondoDoX botnet, tracked through exposed command-and-control logs spanning nine months from March to December 2025, demonstrates a relentless approach to compromising enterprise infrastructure. The malware operates through a multi-stage infection […]
Potential Wallet Phishing Campaign Targets Cardano Users via Eternl Desktop Announcement

A sophisticated phishing campaign is currently circulating within the Cardano community, posing significant risks to users seeking to download the newly announced Eternl Desktop application. The attack leverages a professionally crafted email claiming to promote a legitimate wallet solution designed for secure Cardano token staking and governance participation. The fraudulent announcement references ecosystem-specific incentives, including […]
Apache NuttX Vulnerability Let Attackers to Crash Systems

A newly disclosed use-after-free vulnerability in Apache NuttX RTOS could allow attackers to cause system crashes and unintended filesystem operations, prompting urgent security warnings for users running network-exposed services. The flaw, tracked as CVE-2025-48769 and rated moderate in severity, affects a wide range of NuttX versions and was publicly disclosed on December 31, 2025. The […]
Top 10 High-Risk Vulnerabilities Of 2025 that Exploited in the Wild
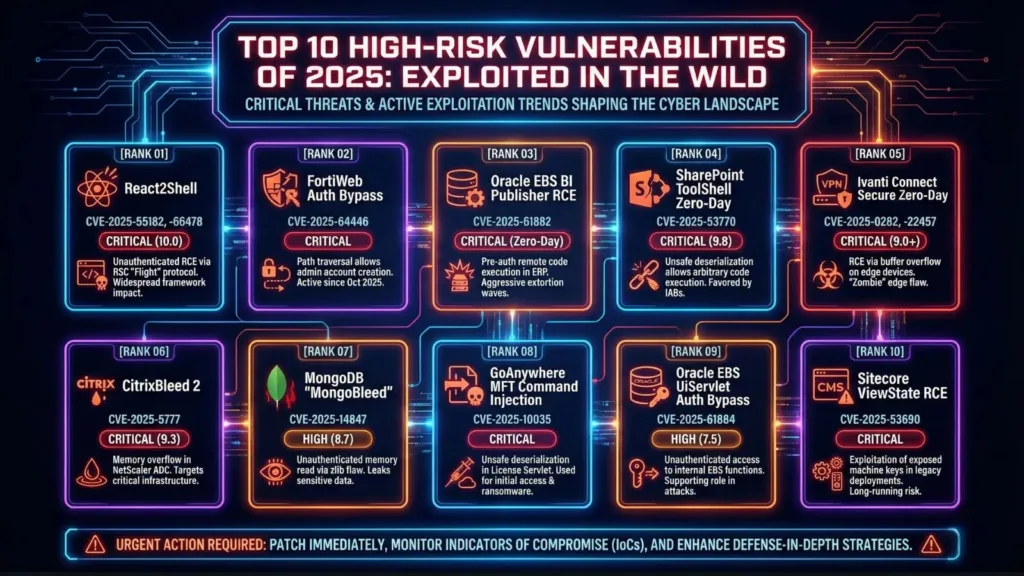
The cybersecurity landscape in 2025 has been marked by an unprecedented surge in critical vulnerabilities, with over 21,500 CVEs disclosed in the first half of the year alone, representing a 16-18% increase compared to 2024. Among these, a select group of vulnerabilities stands out due to their exceptional severity, active exploitation in the wild, and […]
Self-Propagating GlassWorm Weaponizing VS Code Extensions to Attack macOS Users

A new wave of GlassWorm malware has emerged, marking a significant shift in targeting strategy from Windows to macOS systems. This self-propagating worm, distributed through malicious VS Code extensions on the Open VSX marketplace, has already accumulated over 50,000 downloads. The fourth wave introduces several concerning changes including encrypted payloads, hardware wallet trojanization capabilities, and […]
