MongoBleed (CVE-2025-14847) Now Exploited in the Wild: MongoDB Servers at Critical Risk

A high-severity unauthenticated information-leak vulnerability in MongoDB Server, dubbed MongoBleed after the infamous Heartbleed bug, is now being actively exploited in real-world attacks. MongoDB has disclosed CVE-2025-14847, a critical flaw affecting multiple supported and legacy server versions that allows unauthenticated remote attackers to exfiltrate sensitive data and authentication credentials from vulnerable instances. MongoBleed stems from […]
Ubisoft Rainbow Six Siege Servers Breach linked to MongoBleed Vulnerability

The chaos surrounding Ubisoft escalated significantly today as the first group of hackers, previously known for silent exploits, initiated a highly visible and disruptive takeover of Rainbow Six Siege servers. Players worldwide are reporting a massive influx of in-game currency, unwarranted bans, and taunting messages broadcast directly through the game’s administrative feeds. Starting early this […]
87,000+ MongoDB Instances Vulnerable to MongoBleed Flaw Exposed Online PoC Exploit Released

A high-severity vulnerability in MongoDB Server that allows unauthenticated remote attackers to siphon sensitive data from database memory. Dubbed “MongoBleed” due to its automated similarities to the infamous Heartbleed bug, the flaw tracks as CVE-2025-14847 and carries a CVSS score of 7.5. The vulnerability resides in the MongoDB Server’s zlib message decompression implementation. According to […]
Mongobleed PoC Exploit Tool Released for MongoDB Flaw that Exposes Sensitive Data

A proof-of-concept (PoC) exploit dubbed “mongobleed” for CVE-2025-14847, a critical unauthenticated memory leak vulnerability in MongoDB’s zlib decompression handling. Dubbed by its creator Joe Desimone as a way to bleed sensitive server memory, the flaw lets attackers remotely extract uninitialized data without credentials, potentially exposing internal logs, system stats, and more. The vulnerability stems from […]
TeamViewer DEX Vulnerabilities Let Attackers Trigger DoS Attack and Expose Sensitive Data

Multiple critical vulnerabilities in TeamViewer DEX Client’s Content Distribution Service (NomadBranch.exe), formerly part of 1E Client. Affecting Windows versions before 25.11 and select older branches, the flaws stem from improper input validation (CWE-20), potentially enabling attackers on the local network to execute code, crash the service, or leak sensitive data. The most severe issue, CVE-2025-44016 […]
M-Files Vulnerability Let Attacker Capture Session Tokens of Other Active Users

An information disclosure vulnerability in M-Files Server enables authenticated attackers to capture and reuse session tokens from active users. Potentially gaining unauthorized access to sensitive document management systems. The flaw, tracked as CVE-2025-13008, affects multiple versions across different release branches and carries a high-severity CVSS 4.0 base score of 8.6. The vulnerability exists within M-Files […]
TrustWallet Chrome Extension Hacked Users Reporting Millions in Losses
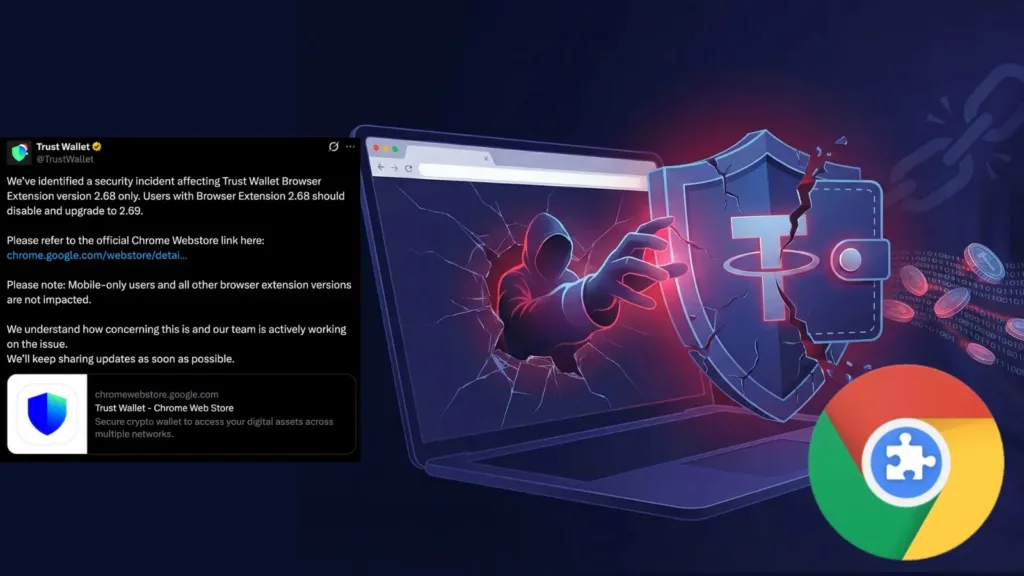
Many Trust Wallet users saw their wallets drained of over $7 million after a security breach in the Chrome browser extension version 2.68.0, released on December 24, 2025. Blockchain investigator ZachXBT first flagged the incident on X, noting a surge in unauthorized outflows from affected addresses shortly after users interacted with the extension. Reports emerged […]
Parrot 7.0 Released with New Penetration Testing and AI Tools

Parrot OS 7.0, codenamed Echo, launches as a complete system rewrite based on Debian 13, bringing KDE Plasma 6, Wayland by default, and fresh penetration testing tools, including a dedicated AI category. This release emphasizes lightweight theming and community-driven spins, marking a pivotal update for ethical hackers and security professionals. The Echo theme draws from […]
Critical Langchain Vulnerability Let attackers Exfiltrate Sensitive Secrets from AI systems

A critical vulnerability in LangChain’s core library (CVE-2025-68664) allows attackers to exfiltrate sensitive environment variables and potentially execute code through deserialization flaws. Discovered by a Cyata researcher and patched just before Christmas 2025, the issue affects one of the most popular AI frameworks with hundreds of millions of downloads. LangChain-core’s dumps() and dumpd() functions failed […]
100+ Cybersecurity Predictions 2026 for Industry Experts as the AI Adapted in the Wild

As artificial intelligence becomes deeply embedded in enterprise operations and cybercriminal arsenals alike, the Cybersecurity Predictions 2026 landscape reveals an unprecedented convergence of autonomous threats, identity-centric attacks, and accelerated digital transformation risks. Industry experts across leading security firms, government agencies, and research institutions have identified over 100 critical predictions that define the year ahead, a year where […]
