Hackers Exploiting Three-Year-Old FortiGate Vulnerability to Bypass 2FA on Firewalls

Cybercriminals are actively abusing a long-patched Fortinet FortiGate flaw from July 2020, slipping past two-factor authentication (2FA) on firewalls and potentially granting unauthorized access to VPNs and admin consoles. Fortinet’s PSIRT team detailed the in-the-wild attacks in a recent blog post, urging admins to audit configurations immediately to avoid compromise. Dubbed FG-IR-19-283 (CVE-2020-12812), the issue […]
Evasive Panda APT Using AitM Attack and DNS Poisoning to Deliver Malware

The Evasive Panda APT group, also known as Bronze Highland, Daggerfly, and StormBamboo, has been running targeted campaigns since November 2022, using advanced techniques to deliver the MgBot malware. The group employs adversary-in-the-middle attacks combined with DNS poisoning to compromise specific victims across multiple industries. Recent findings show that these operations continued until November 2024, […]
Threat Actors Using Weaponized AV-themed Word and PDF Documents to Attack Israeli Organizations
Security researchers at Seqrite Labs have identified a campaign called Operation IconCat, targeting Israeli organizations with weaponized documents designed to look like legitimate security tools. The attacks began in November 2025 and have compromised multiple companies across information technology, staffing services, and software development sectors. The core of this attack relies on a psychological trick: […]
Ransomware Attack on Romanian Waters Authority 1,000+ IT Systems Compromised

Romania’s National Administration “Apele Române” (Romanian Waters) disclosed a severe ransomware attack on December 20, 2025. That compromised approximately 1,000 IT systems across the agency and 10 of its 11 regional water basin administrations. The incident affected critical infrastructure responsible for managing the country’s water resources and hydrotechnical operations. However, operational technologies remained secure throughout […]
Microsoft Teams to Enforce Messaging Safety Defaults Starting January 2026
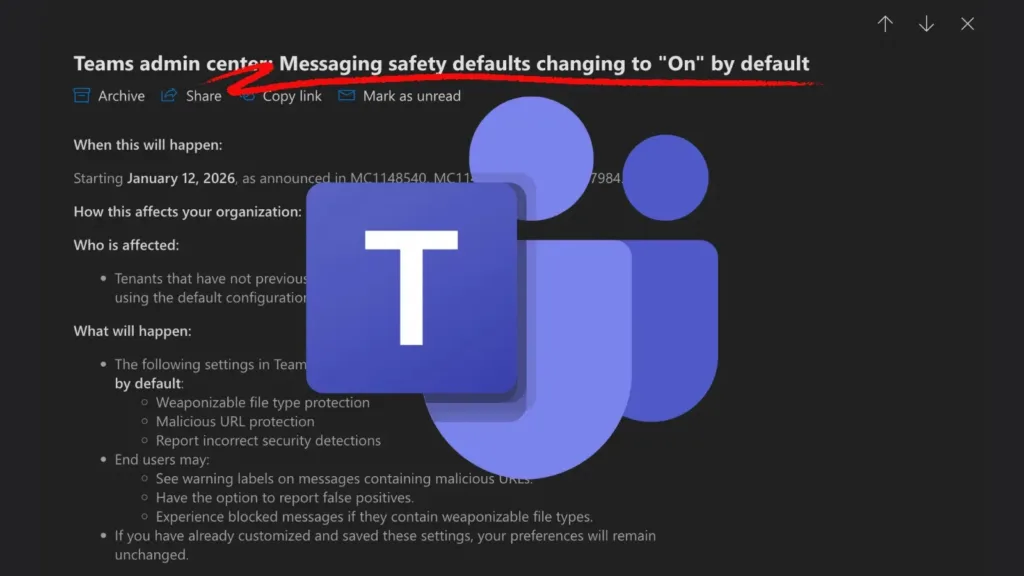
Microsoft is strengthening the security posture of enterprise collaboration by automatically enabling critical messaging safety features in Microsoft Teams. According to a new administrative update, the company will switch several protective settings to “On” by default starting January 12, 2026, affecting tenants who rely on standard configurations. The initiative represents a shift toward “secure-by-default” principles, […]
HardBit 4.0 Ransomware Actors Attack Open RDP and SMB Services to Persist Access
HardBit ransomware continues to evolve as a serious threat to organizations worldwide. The latest version, HardBit 4.0, emerged as an upgraded variant of a strain that has been active since 2022, bringing with it more advanced features and enhanced techniques to avoid detection. This newest iteration represents a significant step forward in the ransomware’s ability […]
CISA Adds Digiever Authorization Vulnerability to KEV List Following Active Exploitation

A critical vulnerability affecting Digiever DS-2105 Pro network video recorders was added to the Known Exploited Vulnerabilities (KEV) catalog on December 22, 2025, following evidence of active exploitation in the wild. CVE-2023-52163 is a missing authorization vulnerability in Digiever DS-2105 Pro devices. That enables attackers to execute unauthorized commands through the time_tzsetup—cgi interface. Attribute Details […]
BlindEagle Hackers Attacking Government Agencies with Powershell Scripts

BlindEagle, a South American threat group, has launched a sophisticated campaign against Colombian government agencies, demonstrating an alarming evolution in attack techniques. In early September 2025, the group targeted a government agency under the Ministry of Commerce, Industry and Tourism (MCIT) using coordinated phishing emails and multi-stage malware delivery. This attack represents a significant escalation […]
PoC Exploit Released for Use-After-Free Vulnerability in Linux Kernels POSIX CPU Timers Implementation

A proof-of-concept (PoC) exploit has been publicly released for CVE-2025-38352, a race condition vulnerability affecting the Linux kernel’s POSIX CPU timer implementation. The flaw enables attackers to trigger use-after-free conditions in kernel memory, potentially leading to privilege escalation and system compromise. CVE-2025-38352 is a race condition that occurs in the kernel’s handle_posix_cpu_timers() function, which processes timer signals […]
DIG AI Darknet AI Tool Enabling Threat Actors to Launch Sophisticated Attacks
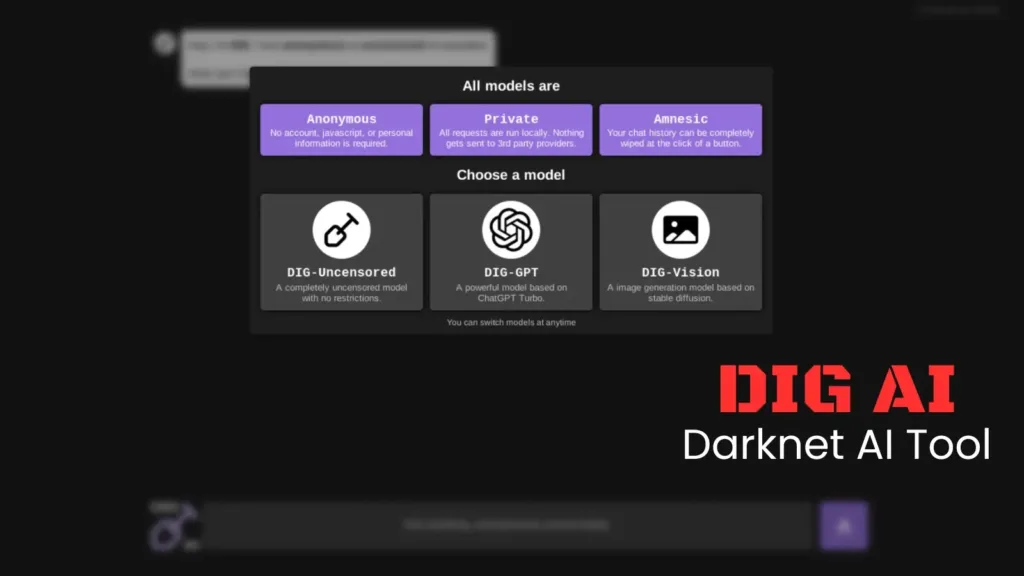
A new and ominous player has emerged in the rapidly expanding landscape of “Shadow AI.” Researchers at Resecurity have identified DIG AI, an uncensored artificial intelligence tool hosted on the darknet that is empowering threat actors to automate cyberattacks, generate illicit content, and bypass the safety guardrails of traditional AI models. First detected on September […]
