KFC Venezuela Alleged Data Breach 1 Million Customer Records Exposed

A threat actor has allegedly breached KFC Venezuela, offering a database containing the personal and order information of over one million customers for sale on a dark web forum. The data, advertised on October 8, 2025, includes a vast amount of sensitive customer details, posing a significant risk of fraud and identity theft to those […]
APT Hackers Exploit ChatGPT to Create Sophisticated Malware and Phishing Emails
A China-aligned advanced persistent threat (APT) group is actively leveraging OpenAI’s ChatGPT platform to develop malware and craft sophisticated spear-phishing emails for its global campaigns. Security firm Volexity tracks the actor as UTA0388 and has analyzed its operations since June 2025, concluding with high confidence that the group uses Large Language Models (LLMs) to automate […]
New Fully Undetectable FUD Android RAT Hosted on GitHub

A sophisticated Android remote access trojan (RAT) has emerged on GitHub, presenting significant security concerns for mobile device users worldwide. The malware, publicly available under the repository “Android-RAT” by user Huckel789, claims to offer fully undetectable (FUD) capabilities that can bypass modern security measures and antivirus detection systems. This malicious software represents a concerning evolution […]
TamperedChef Malware as PDF Editor Harvest Browser Credentials and Allows Backdoor Access

In recent weeks, security teams have observed a surge in malvertising campaigns distributing what appears to be a fully functional PDF editor. Dubbed TamperedChef, this malware masquerades as a legitimate application—AppSuite PDF Editor—leveraging convincing advertisements to lure European organizations and individuals into downloading the installer. Once executed, the installer exhibits expected functionalities for nearly two […]
Ransomware Gangs Leverage Remote Access Tools to Gain Persistence and Evade Defenses

Ransomware operators have shifted from opportunistic malware distribution to highly targeted campaigns that exploit legitimate software for stealth and persistence. Emerging in early 2025, several ransomware families began abusing popular remote access tools—such as AnyDesk and Splashtop—to establish footholds within enterprise networks. By hijacking or silently installing these utilities, adversaries bypass security controls that traditionally […]
New Mic-E-Mouse Attack Let Hackers Exfiltrate Sensitive Data by Exploiting Mouse Sensors
A novel and alarming cybersecurity threat has emerged, turning an ordinary computer peripheral into a sophisticated eavesdropping device. Researchers have detailed a new technique, dubbed the “Mic-E-Mouse” attack, which allows threat actors to exfiltrate sensitive data by exploiting the high-performance optical sensors found in many modern computer mice. This method can covertly capture and reconstruct […]
Researchers Reversed Asgard Malware Protector to Uncover its Antivirus Bypass Techniques

In recent months, security researchers have turned their attention to Asgard Protector, a sophisticated crypter employed by cybercriminals to obfuscate and deploy malicious payloads. First advertised on underground forums in late 2023, Asgard Protector has gained traction among threat actors for its seamless integration with popular C2 platforms such as LummaC2. By wrapping infostealers and […]
New WireTap Attack Break Server SGX To Exfiltrate Sensitive Data
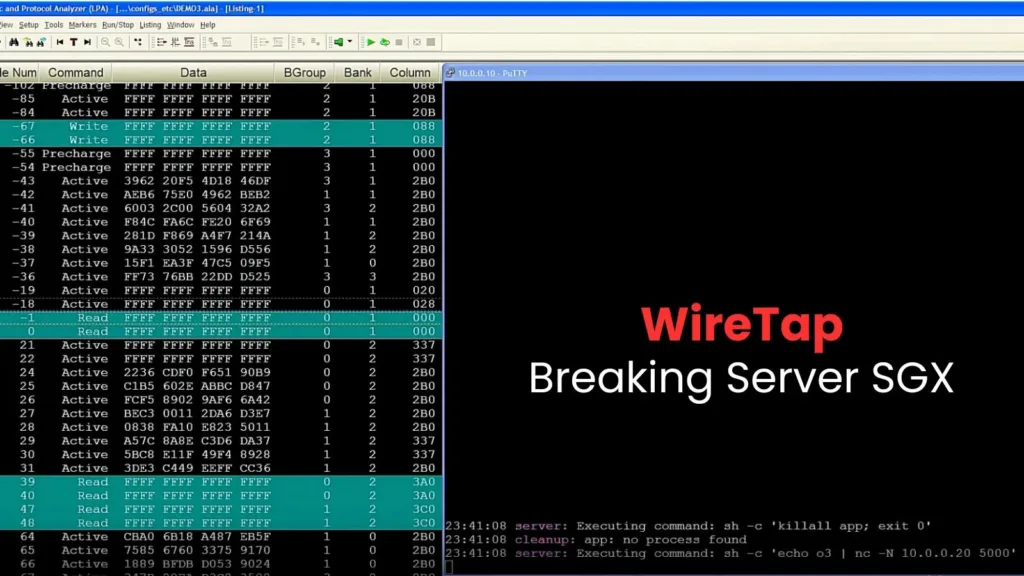
A newly disclosed vulnerability, named the WireTap attack, allows attackers with physical access to break the security of Intel’s Software Guard eXtensions (SGX) on modern server processors and steal sensitive information. A research paper released in October 2025 details how this method can extract cryptographic keys from supposedly secure SGX enclaves using a low-cost setup, […]
Unity Real-Time Development Platform Vulnerability Let Attackers Execute Arbitrary Code

Unity Technologies has issued a critical security advisory warning developers about a high-severity vulnerability affecting its widely used game development platform. The flaw, designated CVE-2025-59489, exposes applications built with vulnerable Unity Editor versions to unsafe file loading attacks that could enable local code execution and privilege escalation across multiple operating systems. The vulnerability stems from […]
Microsoft to Disable Inline SVG Images Display to Outlook for Web and Windows Users

Microsoft has announced a significant security enhancement for Outlook users, implementing the retirement of inline SVG image support across Outlook for Web and the new Outlook for Windows platforms. This change represents a proactive measure to strengthen email security infrastructure and protect users from potential cybersecurity threats. The rollout timeline has been strategically structured to […]
