Chrome Zero-Day Vulnerabilities Actively Exploited in the Wild to Execute Malicious Code

Google has released an urgent security update for its Chrome browser after confirming that two high-severity zero-day vulnerabilities are being actively exploited in the wild. The stable channel has been updated to version 146.0.7680.75/76 for Windows and macOS, and 146.0.7680.75 for Linux, with the rollout expected to reach users over the coming days and weeks. […]
Attackers Hijack Microsoft 365 Accounts Through OAuth Device Code Abuse Without Stealing Passwords
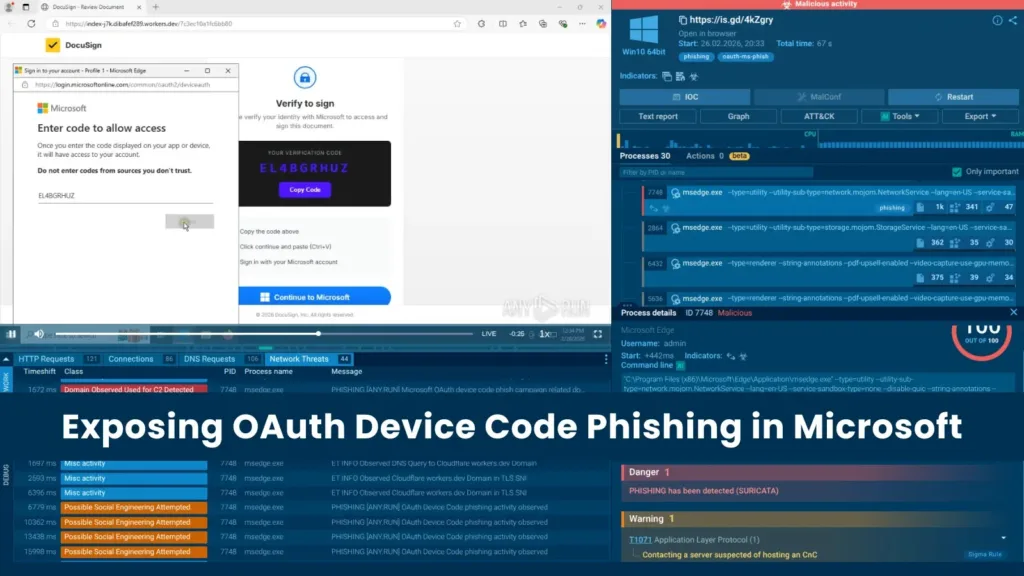
Exposing OAuth Device Code Phishing in Microsoft Analysts at ANY.RUN has identified a sharp spike in phishing campaigns exploiting Microsoft’s OAuth Device Authorization Grant flow, with more than 180 malicious URLs detected within a single week. Unlike conventional credential harvesting, this technique routes victims through legitimate Microsoft authentication pages, making it substantially harder for security […]
Critical MediaTek Vulnerability Lets Attackers Steal Android Phone PINs in 45 Seconds

A critical vulnerability in the MediaTek Dimensity 7300 chipset allows a physical attacker to extract device PINs, decrypt on-device storage, and steal cryptocurrency wallet seed phrases in approximately 45 seconds, raising serious alarms for the roughly 25% of Android users whose devices rely on the affected chip. The vulnerability uncovered by Ledger’s Donjon security research […]
GitLab Security Update Patch for XSS and API DoS Vulnerabilities

GitLab Security Update Patch XSS and API DoS Vulnerabilities GitLab has released urgent security updates for its Community Edition (CE) and Enterprise Edition (EE) to address a wide range of vulnerabilities. The newly released versions 18.9.2, 18.8.6, and 18.7.6 fix a total of 15 security issues, including critical Cross-Site Scripting (XSS) and Denial-of-Service (DoS) flaws. […]
Stryker Cyber Attack Hackers Claim System Breach and Device Wipe

Stryker Cyber Attack On March 11, 2026, global medical technology giant Stryker suffered a devastating cyberattack when Iranian-linked hackers deployed wiper malware to permanently erase data across its network. The breach severely impacted operations at its Cork headquarters and compromised devices worldwide, prompting immediate investigations by internal cybersecurity teams and Microsoft engineers. A massive cyberattack […]
Gogs Vulnerability Enables Attackers to Silently Overwrite Large File Storage Objects

Gogs Vulnerability Overwrite Large File Storage Objects A critical security flaw has been discovered in a popular open-source, self-hosted Git service, allowing attackers to overwrite Large File Storage (LFS) objects secretly. Tracked as CVE-2026-25921, this maximum-severity vulnerability carries a CVSS 3.1 score of 10.0. It creates a severe risk for software supply-chain attacks. The flaw […]
Fortinet Security Update Patch for Multiple Vulnerabilities That Enable Malicious Command Execution

Fortinet released a sweeping security advisory on March 10, 2026, addressing eleven vulnerabilities across its core enterprise products, including FortiManager, FortiAnalyzer, FortiSwitchAXFixed, and FortiSandbox. The flaws range from authentication bypasses and buffer overflows to OS command injection and SQL injection, several of which could allow remote attackers to execute arbitrary commands or escalate privileges on […]
Kali Linux Enhances AI-driven Penetration Testing with Local Ollama, 5ire, and MCP Kali Server

Kali Linux AI-driven Penetration Testing The Kali Linux team has published a new entry in its growing LLM-driven security series, this time eliminating all reliance on third-party cloud services by running large language models entirely on local hardware. The guide demonstrates how security professionals can use natural language to drive penetration testing tools, all processed […]
Signed Malware Masquerading as Teams, Zoom Apps Drops RMM Backdoors

A newly uncovered phishing campaign is actively targeting enterprise users by disguising malware as widely used workplace applications, including Microsoft Teams, Zoom, and Adobe Acrobat Reader. What makes this threat stand out is that the malicious files carry legitimate-looking digital signatures, making them harder for everyday users and even basic security tools to flag. The […]
Hackers Use Fake CleanMyMac Site to Deploy SHub Stealer and Hijack Crypto Wallets

A convincing fake website posing as the popular Mac utility CleanMyMac is actively pushing dangerous macOS malware called SHub Stealer onto unsuspecting users. The site, hosted at cleanmymacos[.]org, has no connection to the real CleanMyMac software or its developers, MacPaw. Once inside a system, SHub Stealer harvests saved passwords, browser data, Apple Keychain contents, cryptocurrency […]
