Researchers Detailed r1z Initial Access Broker OPSEC Failures

U.S. authorities have pulled back the curtain on “r1z,” an initial access broker who quietly sold gateways into corporate networks around the world. Operating across popular cybercrime forums, he offered stolen VPN credentials, remote access to enterprise environments, and custom tools designed to bypass security controls. His activity fed the ransomware supply chain by giving […]
New ClearFake Campaign Leveraging Proxy Execution to Run PowerShell Commands via Trusted Window Feature

ClearFake has entered a new and more dangerous phase, turning a familiar fake CAPTCHA scam into a highly evasive malware delivery chain. Across hundreds of hacked websites, visitors now see what looks like a routine verification challenge, but behind the scenes the page is preparing to launch hidden code. Victims only need to follow simple […]
Hackers Weaponized 2,500+ Security Toolsto Terminate Endpoint Protection Before Deploying Ransomware

A large-scale campaign is turning a trusted Windows security driver into a weapon that shuts down protection tools before ransomware and remote access malware are dropped. The attacks abuse truesight.sys, a kernel driver from Adlice Software’s RogueKiller antivirus, and use more than 2,500 validly signed variants to quietly disable endpoint detection and response (EDR) and […]
New Magecart Attack Inject Malicious JavaScript to Skim Payment Data

A new Magecart-style campaign has emerged, targeting online shoppers through malicious JavaScript code designed to steal payment information directly from ecommerce websites. The attack works by injecting hidden scripts into compromised shopping sites, allowing attackers to intercept sensitive data when customers enter their credit card details during checkout. Magecart attacks represent a significant threat to […]
Critical Oracle WebLogic Server Proxy Vulnerability Lets Attackers Compromise the Server

Oracle has disclosed a severe security vulnerability affecting its Fusion Middleware suite, specifically targeting the Oracle HTTP Server and the Oracle WebLogic Server Proxy Plug-in. Assigned CVE-2026-21962, this flaw carries the maximum severity rating and poses an immediate threat to enterprise environments that use these proxy components. The vulnerability stems from a defect in how […]
New Study Shows GPT-5.2 Can Reliably Develop Zero-Day Exploits at Scale

A groundbreaking experiment has revealed that advanced language models can now create working exploits for previously unknown security vulnerabilities. Security researcher Sean Heelan recently tested two sophisticated systems built on GPT-5.2 and Opus 4.5, challenging them to develop exploits for a zero-day flaw in the QuickJS Javascript interpreter. The results point to a significant shift […]
WhisperPair Attack Allows Hijacking of Laptops, Earbuds Without User Consent Millions Affected

A critical vulnerability in Google’s Fast Pair protocol that allows attackers to hijack Bluetooth audio accessories and track users without their knowledge or consent. Security researchers from KU Leuven have uncovered a vulnerability, tracked as CVE-2025-36911 and dubbed WhisperPair, that affects hundreds of millions of wireless earbuds, headphones, and speakers from major manufacturers. Including Sony, […]
Remcos RAT Masquerade as VeraCrypt Installers Steals Users Login Credentials

A sophisticated malware campaign targeting South Korean users has emerged, distributing the Remcos remote access trojan (RAT) through deceptive installers disguised as legitimate VeraCrypt encryption software. This ongoing attack campaign primarily focuses on individuals connected to illegal online gambling platforms, though security experts warn that everyday users downloading encryption tools may also fall victim to […]
Free Converter Apps that Convert your Clean System to Infected in Seconds
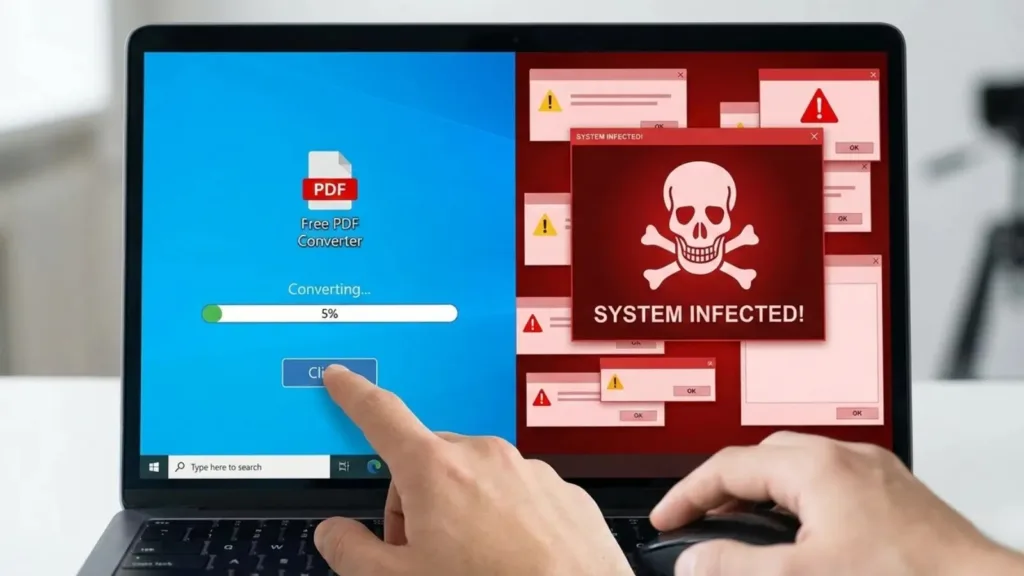
Malicious file converter applications distributed through deceptive advertisements are infecting thousands of systems with persistent remote access trojans (RATs). These seemingly legitimate productivity tools perform their advertised functions while secretly installing backdoors that give attackers continuous access to victim computers. Nextron Systems found that the infection chain typically begins with malicious Google advertisements placed on […]
Redmi Buds Vulnerability Allow Attackers Access Call Data and Trigger Firmware Crashes

Security researchers have uncovered significant vulnerabilities in the firmware of Xiaomi’s popular Redmi Buds series, specifically affecting models ranging from the Redmi Buds 3 Pro up to the latest Redmi Buds 6 Pro. The discovery highlights critical flaws in the Bluetooth implementation of these devices, allowing attackers to access sensitive information or force the devices […]
