Microsoft January 2026 Security Update Causes Credential Prompt Failures in Remote Desktop Connections

Microsoft has released an out-of-band emergency update to resolve a critical issue affecting Remote Desktop connections on Windows client devices. The problem emerged immediately following the installation of the January 2026 security update, identified as KB5074109. Administrators and users reported widespread credential prompt failures when attempting to sign in via the Windows App, significantly disrupting […]
Mandiant Releases Rainbow Tables Enabling NTLMv1 Admin Password Hacking
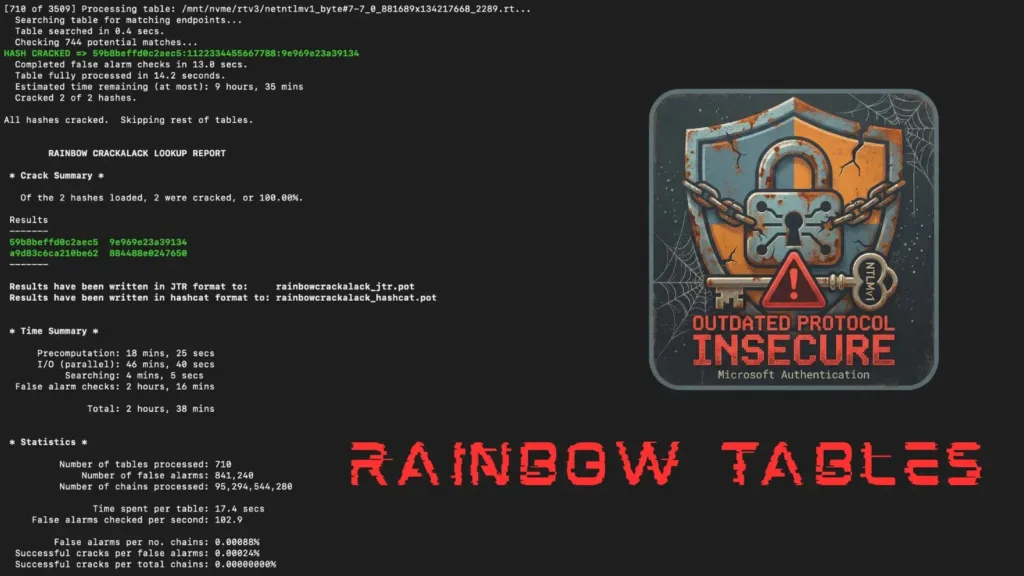
Google-owned Mandiant has publicly released a comprehensive dataset of Net-NTLMv1 rainbow tables, marking a significant escalation in demonstrating the security risks of legacy authentication protocols. The release underscores an urgent message: organizations must immediately migrate away from Net-NTLMv1, a deprecated protocol that has been cryptographically broken since 1999 and widely known to be insecure since […]
Lets Encrypt has made 6-day IP-based TLS certificates Generally Available

Let’s Encrypt, a key provider of free TLS certificates, has rolled out short-lived and IP address-based certificates for general use. These new options became available starting in early 2026, addressing long-standing issues in certificate security. Short-lived certificates last just 160 hours, about six and a half days, while IP-based ones tie directly to IP addresses […]
Argus Python-powered Toolkit for Information Gathering and Reconnaissance

Argus is a comprehensive Python-based toolkit designed for reconnaissance tasks in cybersecurity. The developers recently released version 2.0, expanding it to include 135 modules. This tool consolidates network analysis, web app scanning, and threat intelligence into one interface. Users access modules through an interactive CLI that supports searching, favorites, and batch runs. Network and infrastructure […]
Googles Vertex AI Vulnerability Enables Low-Privileged Users to Gain Service Agent Roles
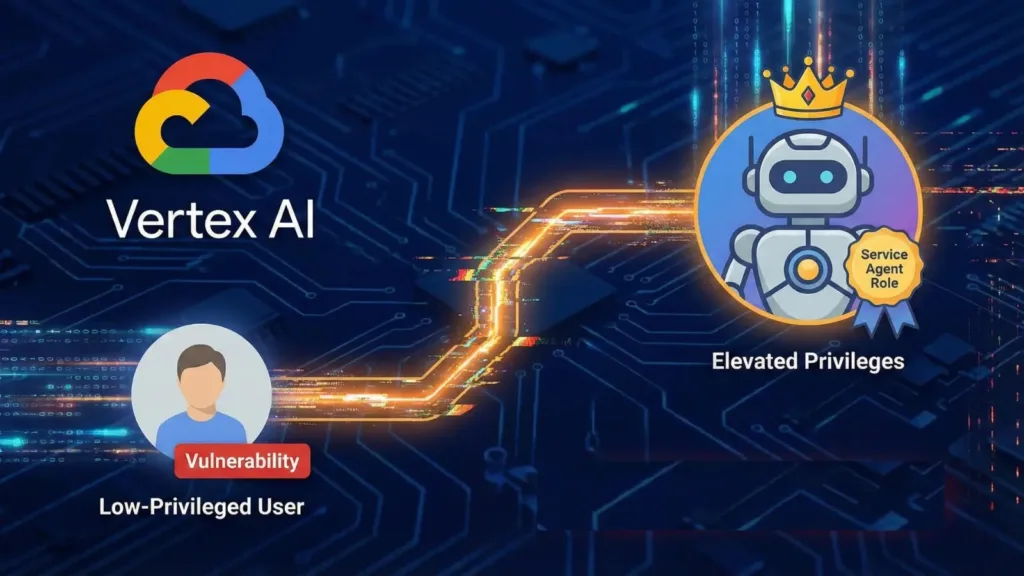
Google’s Vertex AI contains default configurations that allow low-privileged users to escalate privileges by hijacking Service Agent roles. XM Cyber researchers identified two attack vectors in the Vertex AI Agent Engine and Ray on Vertex AI, which Google deemed “working as intended. Service Agents are managed identities that Google Cloud attaches to Vertex AI instances […]
Researchers Gain Access to StealC Malware Command-and-Control Systems

Security researchers successfully exploited vulnerabilities in the StealC malware infrastructure, gaining access to operator control panels and exposing a threat actor’s identity through their own stolen session cookies. The breach highlights critical security failures in criminal operations built around credential theft. XSS Vulnerability Exposes StealC Operators StealC, an information-stealing malware operating under a Malware-as-a-Service model […]
Windows 11 PCs Fail to Shut Down After January Security Update

Microsoft’s January 13, 2026, security update for Windows 11 has triggered a frustrating bug: affected PCs refuse to shut down or hibernate, instead restarting. The issue is caused by KB5073455, which targets OS Build 22621.6491 on Windows 11 version 23H2. It was first reported on January 15 and arises from interference with Secure Launch, a […]
Cisco 0-Day RCE Secure Email Gateway Vulnerability Exploited in the Wild

Cisco has confirmed active exploitation of a critical zero-day remote code execution vulnerability in its Secure Email Gateway and Secure Email and Web Manager appliances. Tracked as CVE-2025-20393, the flaw allows unauthenticated attackers to execute arbitrary root-level commands via crafted HTTP requests to the Spam Quarantine feature. The vulnerability stems from insufficient validation of HTTP […]
Google Rolls Out Long-Awaited @gmail.com Email Change Featurefor Users

Google is gradually rolling out the ability to change the @gmail.com email address associated with a Google Account to a new @gmail.com address. This feature, previously unavailable, addresses a common pain point for users who regret their original username choice but didn’t want to abandon years of emails, photos, and data. We already notified you […]
Hackers Abusing Legitimate Cloud and CDN Platforms to Host Phishing Kits

Threat actors are increasingly using trusted cloud and content delivery network platforms to host phishing kits, creating major detection challenges for security teams. Unlike traditional phishing campaigns that rely on newly registered suspicious domains, these attacks use legitimate infrastructure from providers like Google, Microsoft Azure, and AWS CloudFront. This approach allows hackers to bypass many […]
