Cloudflare Acquires Human Native to Strengthen AI Data Security

Cloudflare, the San Francisco-based cybersecurity and internet infrastructure giant, has acquired Human Native, a UK-based AI data marketplace. The deal aims to empower content creators with control over their data in the generative AI era, addressing rising tensions around web scraping and bot traffic. Human Native specializes in converting unstructured multimedia videos, articles, and more […]
Chinese Threat Actors Hosted 18,000 Active C2 Servers Across 48 Hosting Providers

Threat actors linked to Chinese hosting infrastructure have established a massive network of over 18,000 active command-and-control servers across 48 different hosting providers in recent months. This widespread abuse highlights a serious issue in how malicious infrastructure can hide within trusted networks and cloud services. Traditional threat hunting methods that focus on individual IP addresses […]
Stealthy CastleLoader Malware Attacking US Government Agencies and Critical Infrastructure
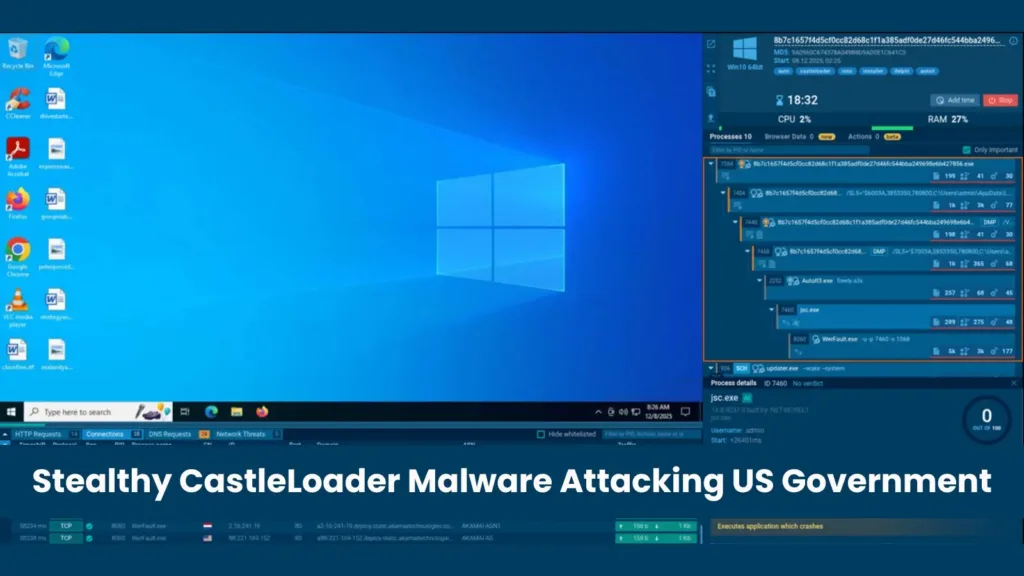
A sophisticated malware loader known as CastleLoader has emerged as a critical threat to US government agencies and critical infrastructure organizations. First identified in early 2025, this stealthy malware has been used as the initial access point in coordinated attacks targeting multiple sectors including federal agencies, IT firms, logistics companies, and essential infrastructure providers across […]
Top 12 Best Open Source Intelligence Tools (OSINT Tools) for Penetration Testing 2026

We all know very well that getting or gathering any information by using various tools becomes really easy. In this article, we have discussed various OSINT tools, as if we search over the internet, then there will be many different pages to pop out. But the most problematic thing is to gather different information from […]
Microsoft Patch Tuesday January 2026 114 Vulnerabilities Fixed Including 3 Zero-days

CVE-2026-20822 Windows Graphics Component Elevation of Privilege Vulnerability Elevation of Privilege CVE-2026-20876 Windows Virtualization-Based Security (VBS) Enclave Elevation of Privilege Vulnerability Elevation of Privilege CVE-2026-20944 Microsoft Word Remote Code Execution Vulnerability Remote Code Execution CVE-2026-20953 Microsoft Office Remote Code Execution Vulnerability Remote Code Execution CVE-2026-20955 Microsoft Excel Remote Code Execution Vulnerability Remote Code Execution CVE-2026-20854 […]
Multi-Stage Windows Malware Invokes PowerShell Downloader Using Text-based Payloads Using Remote Host

Security researchers have identified a sophisticated multi-stage Windows malware campaign called SHADOW#REACTOR that represents a significant evolution in delivery mechanisms for remote access tools. The campaign demonstrates how threat actors combine traditional scripting techniques with modern obfuscation methods to bypass security defenses. The infection begins with an obfuscated Visual Basic Script that initiates a carefully […]
100,000+ n8n Instances Exposed to Internet Vulnerable to RCE Attacks
A critical vulnerability affecting the popular n8n workflow automation platform has put over 100,000 internet-exposed instances at severe risk. Security researchers from The Shadowserver Foundation discovered that 105,753 unique n8n instances are vulnerable to remote code execution (RCE) attacks through CVE-2026-21858. n8n is a workflow automation platform that connects various applications, services, and databases. Organizations […]
Hackers Infiltrated n8ns Community Node Ecosystem With a Weaponized npm Package

Attackers have successfully infiltrated n8n’s community node ecosystem using a malicious npm package disguised as a legitimate Google Ads integration tool. The attack reveals a critical vulnerability in how workflow automation platforms handle third-party integrations and user credentials. The malicious package, named n8n-nodes-hfgjf-irtuinvcm-lasdqewriit, tricked developers into entering their Google Ads OAuth credentials through a seemingly […]
InvisibleJS Tool Hides Executable ES Modules in Empty Files Using Zero-Width Steganography
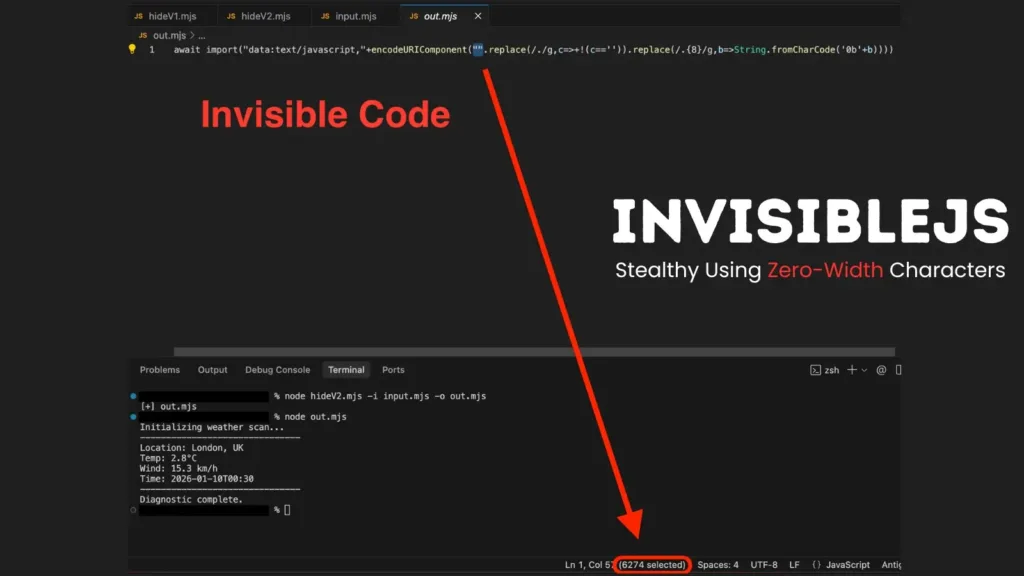
InvisibleJS, a new open-source tool that conceals JavaScript code using invisible zero-width Unicode characters, raises alarms about potential misuse in malware campaigns. InvisibleJS, hosted on GitHub by developer With alias oscarmine, employs steganography to embed source code into seemingly blank files. The process converts JavaScript into binary strings, mapping 0s to Zero Width Space (U+200B) […]
Beware of Weaponized Employee Performance Reports that Deploys Guloader Malware

Cybersecurity threats continue to evolve with attackers using more creative social engineering techniques to target organizations. A recent threat has emerged involving the Guloader malware, which is being disguised as employee performance reports to trick users into downloading and executing malicious files. This sophisticated attack vector exploits human trust and workplace familiarity to distribute dangerous […]
