New CometJacking Attack Let Attackers Turn Perplexity Browser Against You in One Click
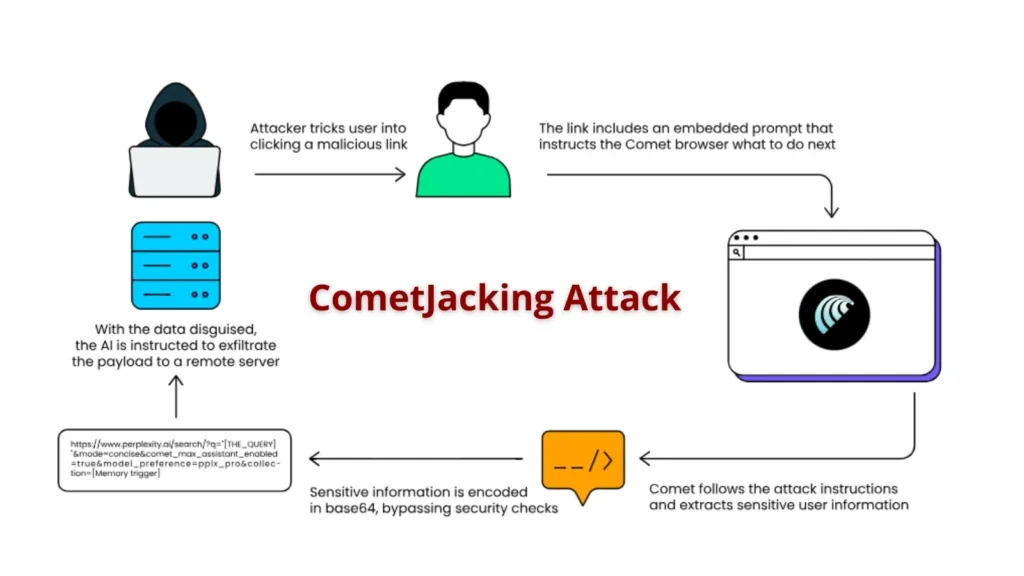
A groundbreaking cybersecurity vulnerability has emerged that transforms Perplexity’s AI-powered Comet browser into an unintentional collaborator for data theft. Security researchers at LayerX have discovered a sophisticated attack vector dubbed “CometJacking” that enables malicious actors to weaponize a single URL to extract sensitive user data without requiring any traditional credential theft or malicious webpage content. […]
Discord Data Breach Customers Personal Data and Scanned Photo IDs leaked

A data breach at a third-party customer service provider has exposed the personal data of some Discord users, including names, email addresses, and a small number of scanned government-issued photo IDs. The incident did not compromise Discord’s main systems, and the unauthorized access was limited to data handled by the company’s support teams. Discord announced […]
Top 10 Best Supply Chain Intelligence Security Companies in 2025

The digital world continues to face growing threats around software vulnerabilities, data breaches, and cyber supply chain attacks. As companies rely more heavily on open-source software, third-party code, and cloud-native applications, the need for supply chain intelligence security solutions has never been greater. In 2025, organizations must adopt highly reliable platforms that provide visibility, compliance, […]
New Android Spyware Attacking Android Users Mimic as Signal and ToTok Apps

In recent months, security teams have observed a surge in Android spyware campaigns that prey on privacy-conscious users by masquerading as trusted messaging apps. These malicious payloads exploit users’ trust in Signal and ToTok, delivering trojanized applications that request extensive permissions under the guise of enhanced functionality. Initial distribution relies on phishing websites and fake […]
Threat Actors Pose as Government Officials to Attack Organizations with StallionRAT

In recent months, a sophisticated campaign dubbed Cavalry Werewolf has emerged, targeting government and critical infrastructure organizations across Russia and neighboring regions. Adversaries initiated these attacks by sending meticulously crafted phishing emails that impersonate officials from Kyrgyz government agencies. These emails contain malicious RAR archives, which deploy a suite of custom tools, including the FoalShell […]
New AmCache EvilHunter Tool For Detecting Malicious Activities in Windows Systems
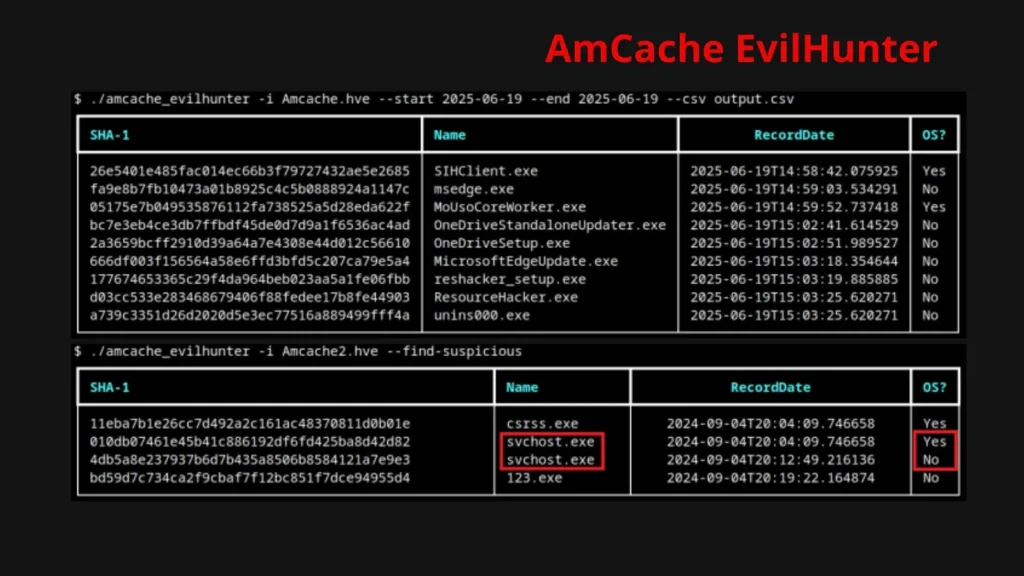
AmCache plays a vital role in identifying malicious activities in Windows systems. This tool allows the identification of both benign and malicious software execution on a machine. Managed by the operating system and virtually tamper-proof, AmCache data endures even when malware auto-deletes itself, making it indispensable in incident response. AmCache stores SHA-1 hashes of executed […]
Red Hat Data Breach Threat Actors Claim Breach of 28K Private GitHub Repositories

An extortion group known as the Crimson Collective claims to have breached Red Hat’s private GitHub repositories, making off with nearly 570GB of compressed data from 28,000 internal repositories. This data theft is being regarded as one of the most significant breaches in technology history, involving the unauthorized extraction of source code and sensitive confidential […]
Chrome Security Update Patch for 21 Vulnerabilities that Allows Attackers to Crash Browser

Google has released Chrome 141 to address 21 security vulnerabilities, including critical flaws that could allow attackers to crash browsers and potentially execute malicious code. The update, rolling out across Windows, Mac, and Linux platforms, patches several high-severity vulnerabilities that pose significant risks to user security. The most severe vulnerability addressed is CVE-2025-11205, a heap […]
Hackers use Weaponized Microsoft Teams Installer to Compromise Systems With Oyster Malware

A sophisticated malvertising campaign is using fake Microsoft Teams installers to compromise corporate systems, leveraging poisoned search engine results and abused code-signing certificates to deliver the Oyster backdoor malware. The attack was neutralized by Microsoft Defender’s Attack Surface Reduction (ASR) rules, which blocked the malware from establishing contact with its command-and-control server. The multi-stage attack […]
Apache Airflow Vulnerability Exposes Sensitive Details to Read-Only Users

A critical security flaw has emerged in Apache Airflow 3.0.3, exposing sensitive connection information to users with only read permissions. The vulnerability, tracked as CVE-2025-54831 and classified as “important” severity, fundamentally undermines the platform’s intended security model for handling sensitive data within workflow connections. Apache Airflow version 3.0 introduced significant changes to how sensitive information […]
