New Udados Botnet Launches Massive HTTP Flood DDoS Attacks Targeting Tech Sector
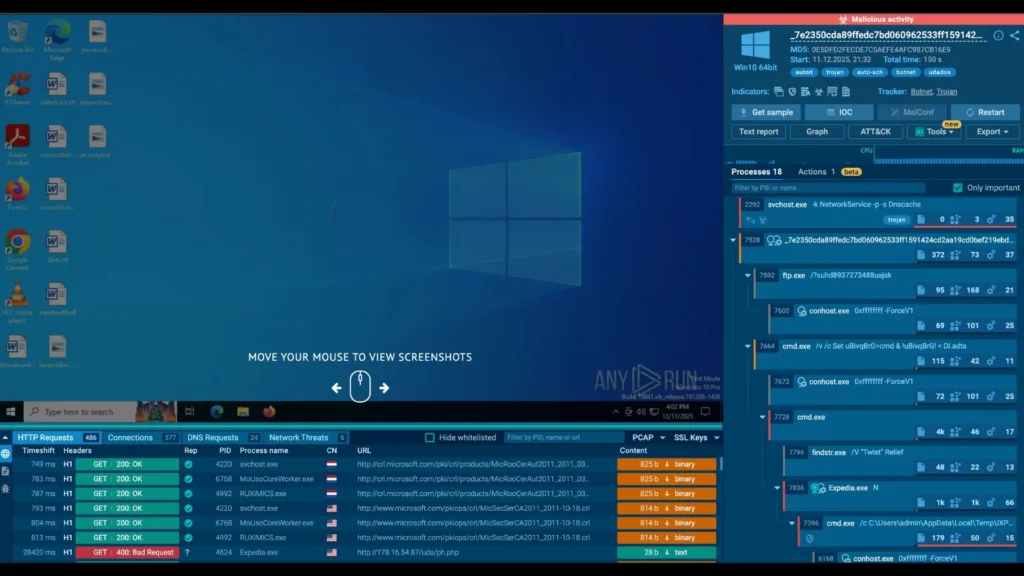
A newly identified botnet malware family, dubbed “Udados,” has emerged as a significant threat to the Technology and Telecommunications sectors, orchestrating high-volume HTTP flood Distributed Denial-of-Service (DDoS) attacks. According to ANY.RUN sandbox analysis, the botnet leverages infected hosts to execute sustained denial-of-service campaigns designed to disrupt business continuity by overwhelming target servers with legitimate-looking traffic. […]
Hackers Exploiting RMM Tools LogMeIn and PDQ Connect to Deploy Malware as a Normal Program

Cybercriminals are now exploiting remote monitoring and management tools to spread dangerous malware while avoiding detection by security systems. The attack campaign targets users who download what appears to be popular software, such as Notepad++, 7-Zip, or ChatGPT, from fake websites. Instead of getting the real program, victims unknowingly install LogMeIn Resolve or PDQ Connect, […]
New Wave of Steganography Attacks: Hackers HidingXWormin PNGs
ANY.RUN experts recently uncovered a new XWorm campaign that uses steganography to conceal malicious payloads inside seemingly harmless PNG images. What appears to be an ordinary graphic actually contains encrypted loaders that execute entirely in memory, allowing the malware to bypass most traditional detection methods and signature-based defenses. Let’s break down how this attack works and what analysts and hunters should look […]
Apple Patches Multiple Critical Vulnerabilities in iOS 26.1 and iPadOS 26.1
Apple released iOS 26.1 and iPadOS 26.1, addressing multiple vulnerabilities that could lead to privacy breaches, app crashes, and potential data leaks for iPhone and iPad users. The update targets devices starting from the iPhone 11 series and various iPad models, including the iPad Pro (3rd generation 12.9-inch and later), iPad Pro 11-inch (1st generation […]
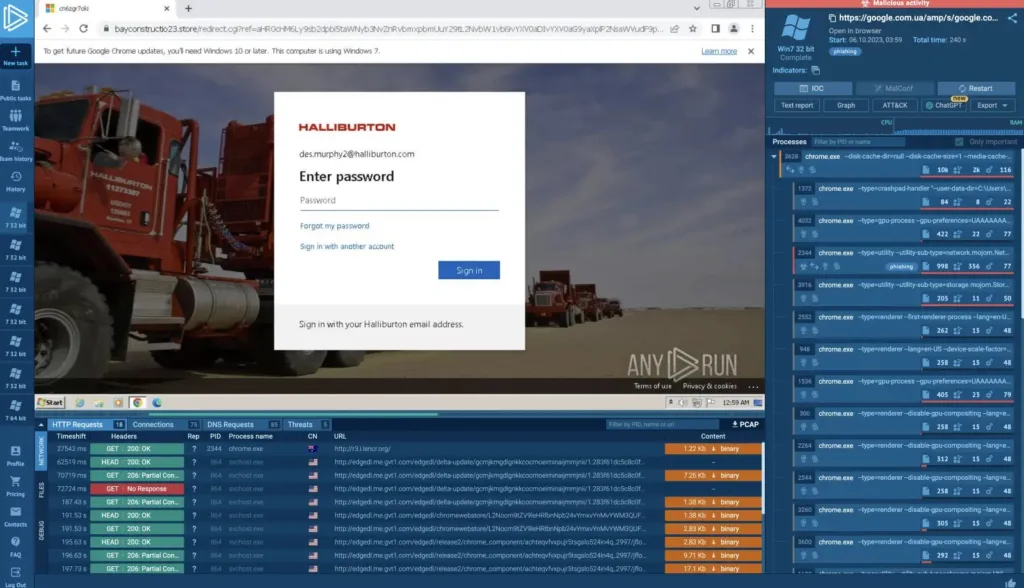
New TruffleNet BEC Campaign Leverages AWS SES Using Stolen Credentials to Compromise 800+ Hosts

Identity compromise has become one of the most significant threats facing cloud infrastructure, particularly when attackers gain access to legitimate credentials. These valid access keys enable adversaries to bypass traditional security defenses, creating opportunities for widespread exploitation. Amazon Web Services environments have witnessed a surge in such attacks, with the Simple Email Service emerging as […]
Hackers Can Manipulate Claude AI APIs with Indirect Prompts to Steal User Data
Hackers can exploit Anthropic’s Claude AI to steal sensitive user data. By leveraging the model’s newly added network capabilities in its Code Interpreter tool, attackers can use indirect prompt injection to extract private information, such as chat histories, and upload it directly to their own accounts. This revelation, detailed in Rehberger’s October 2025 blog post, […]
Hackers Can Inject Malicious Code into Antivirus Processes to Create a Backdoor

A new technique enables attackers to exploit antivirus software by injecting harmful code directly into the antivirus processes. This approach makes it easier for them to evade detection and compromise the security that antivirus software is designed to provide. This method, detailed by cybersecurity researcher Two Seven One Three on X (@TwoSevenOneT), involves cloning protected […]
Microsoft Defender Vulnerabilities Allow Attackers to Bypass Authentication and Upload Malicious Files

Critical flaws uncovered in the network communication between Microsoft Defender for Endpoint (DFE) and its cloud services, allowing post-breach attackers to bypass authentication, spoof data, disclose sensitive information, and even upload malicious files to investigation packages. These vulnerabilities, detailed in a recent analysis by InfoGuard Labs, highlight ongoing risks in endpoint detection and response (EDR) […]
New Chaosbot Leveraging CiscoVPN and Active Directory Passwords to Execute Network Commands

ChaosBot surfaced in late September 2025 as a sophisticated Rust-based backdoor targeting enterprise networks. Initial investigations revealed that threat actors gained entry by exploiting compromised CiscoVPN credentials coupled with over-privileged Active Directory service accounts. Once inside, ChaosBot was stealthily deployed via side-loading techniques using the legitimate Microsoft Edge component identity_helper.exe from the C:UsersPublicLibraries directory. The […]
Threat Actors Exploiting SonicWall SSL VPN Devices in Wild to Deploy Akira Ransomware

Threat actors have reemerged in mid-2025 leveraging previously disclosed vulnerabilities in SonicWall SSL VPN appliances to deploy Akira ransomware on enterprise networks. Beginning in July, multiple incidents of initial access via unpatched SonicWall devices were reported across North America and EMEA. Attackers exploited CVE-2024-40766, an access control flaw in SonicOS versions up to 7.0.1-5035, enabling […]
